In August 2023, a vulnerability in the HTTP/2 protocol, known as CVE-2023-44487 or "Rapid Reset," was discovered. This article provides an in-depth understanding of how CVE-2023-44487 works, its impact on HTTP/2, and offers 4 mitigation strategies to defend against this vulnerability.

Understanding CVE-2023-44487
HTTP/2 introduced several improvements to the HTTP network protocol, including stream multiplexing, which allows multiple streams to be opened over a single TCP connection. However, the Rapid Reset vulnerability exploits the protocol's stream cancellation mechanism using RST_STREAM frames.
When browsing a website that supports HTTP/2, a single connection can be used to fetch multiple resources, improving browsing efficiency. However, this streaming capability can be challenging as it allows a single connection to generate numerous requests. To address this, HTTP/2 provides a mechanism to limit the number of active concurrent streams to prevent clients from overburdening the server.
Exploiting the Rapid Reset vulnerability involves an attacker sending an RST_STREAM frame immediately after sending a request frame. This instructs the server to start processing the request but rapidly cancels it. Although the request is canceled, the HTTP/2 connection remains open, allowing new streams to be created. As a result, the server needs to allocate resources and perform tasks such as parsing the query and decompressing the header for each canceled request, leading to a denial-of-service (DoS) scenario.
The Impact of CVE-2023-44487
The Rapid Reset vulnerability has resulted in unprecedented distributed denial-of-service (DDoS) attacks. Major web service providers like Google, AWS, and Cloudflare have reported massive attacks, reaching peak request rates in the hundreds of millions per second. These attacks have been generated using relatively small botnets, highlighting the severity of the vulnerability, capable of overwhelming servers with ease.
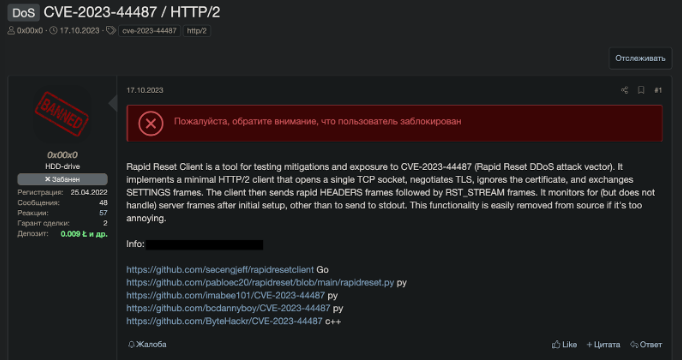
Cybercriminals sharing a proof of concept for CVE-2023-44487
The sharing of proof-of-concepts by cybercriminals suggests an increase in malicious activity, emphasizing the need for optimization strategies related to this vulnerability. Cybercriminals have been actively exploiting the Rapid Reset vulnerability, using it to launch DDoS attacks against organizations. The ease of exploitation and the potential for significant damage have made this vulnerability a prime target for cybercriminals.
4 Ways to Mitigate CVE-2023-44487
To effectively defend against the HTTP/2 Rapid Reset vulnerability (CVE-2023-44487), organizations should implement the following mitigation strategies:
1. Connection Tracking: Closely monitor connection statistics, including the number of active streams, stream creation rate, and stream cancellation rate. Identify abusive HTTP/2 connections and implement business logic to assess the usefulness of each connection based on factors such as request content and client behavior. Close connections displaying abusive patterns to mitigate the impact of the Rapid Reset attack.
2. Rate Limiting: Implement rate limiting mechanisms at the connection and stream level to control traffic flow. Identify suspicious traffic patterns, such as a high number of rapidly canceled streams or requests from known malicious IP addresses, and block them. Use techniques like adaptive throttling or request queuing to dynamically adjust rate limits based on the severity of the attack and available server resources.
3. Apache Recommendations: For organizations using Apache web servers, configure built-in measures to limit excessive load, such as the MaxRequestWorkers and MaxConnectionsPerChild directives, based on server capacity and expected traffic. Upgrade the libnghttp2 dependency of the mod_http2 module to version 1.57.0 or later, which includes fixes for the Rapid Reset vulnerability. Consider implementing additional security modules or plugins, such as mod_security or mod_evasive, to enhance protection against HTTP/2 attacks.
4. Nginx Recommendations: For organizations using Nginx web servers, verify that the default keepalive limit (keepalive_requests) is not substantially increased, as this may make the server more susceptible to Rapid Reset attacks. If non-default configurations with higher keepalive limits are used, rebuild the Nginx binaries from the latest codebase, including a patch to prevent excessive resource consumption caused by the vulnerability. Configure the http2_max_concurrent_streams directive to limit the number of concurrent streams allowed per connection based on server capacity and expected traffic patterns.
Additional Note
This vulnerability does not affect HAProxy users because of protective measures implemented in HAProxy 1.9 and carried forward in subsequent versions. These measures improve how HAProxy handles HTTP/2 protocol stream multiplexing to better counter malicious attacks, such as the Rapid Reset Attack. Instead of only counting known, established streams at the protocol level, HAProxy 1.9 and later versions count allocated resources and keep a stream in its accounting until resources are fully released.
Frequently Asked Questions
1. What is the HTTP/2 Rapid Reset vulnerability?
The HTTP/2 Rapid Reset vulnerability, also known as CVE-2023-44487, is a security vulnerability in the HTTP/2 protocol that allows attackers to launch DDoS attacks.
2. How does the Rapid Reset vulnerability work?
A: The vulnerability exploits the stream cancellation mechanism using RST_STREAM frames, allowing an attacker to rapidly cancel requests and consume server resources, leading to a DoS scenario.
3. What are some common symptoms of the HTTP/2 Rapid Reset vulnerability?
Symptoms may include high CPU usage, increased memory consumption, and slow response times due to excessive resource allocation caused by cancelled requests.
4. How can I protect my web service from the Rapid Reset vulnerability?
Implement connection tracking, rate limiting, and Apache or Nginx-specific recommendations to prevent abusive connections and limit traffic flow.
How Can Qrator.AntiDDoS Help?
Qrator Labs' industry-leading DDoS mitigation solution, Qrator.AntiDDoS, is well-equipped to defend against the HTTP/2 Rapid Reset vulnerability (CVE-2023-44487). Our global filtering network, with 15 scrubbing centers and a throughput of more than 4 Tbps, ensures comprehensive protection against all types of DDoS attacks, including those exploiting the Rapid Reset vulnerability.
Don't let the HTTP/2 Rapid Reset vulnerability put your web services at risk. Choose Qrator Labs and Qrator.AntiDDoS for industry-leading DDoS protection and peace of mind. Contact our sales team today to learn more about how we can help secure your online presence and protect your business from the threat of DDoS attacks.
