Established in 2009, Qrator Labs provides DDoS mitigation services and is an acknowledged expert in this industry. The Qrator Labs expert team has been conducting research in the field of DDoS protection since 2006 and has been continuously improving algorithms, technologies and techniques of DDoS attack mitigation. In 2010 the company launched its own Qrator traffic filtration network as a technological basis for the commercial service dedicated to the protection of network services from similar threats. Algorithms and technologies used for mitigation of attacks against the web services of its customers are the company’s specialty and focus.

Abstract
This paper is intended to explain how best to improve the resiliency of a given network operator against Distributed Denial of Service (DDoS) attacks. The paper provides an overview of DDoS attacks and mitigation techniques including the capabilities of Qrator.Ingress.
The document is targeted at IT decision makers and security personnel who are familiar with basic concepts in the area of networking and security.
Introduction
A Distributed Denial of Service (DDoS) attack can make the targeted resource (application, website or entire network) unavailable to end users. To achieve this objective, attackers employ a variety of techniques to occupy network or other resources and disrupt access for legitimate users.
To carry out a DDoS attack, an attacker uses multiple sources — which may be compromised or controlled by a group of collaborators — in coordination against a target.
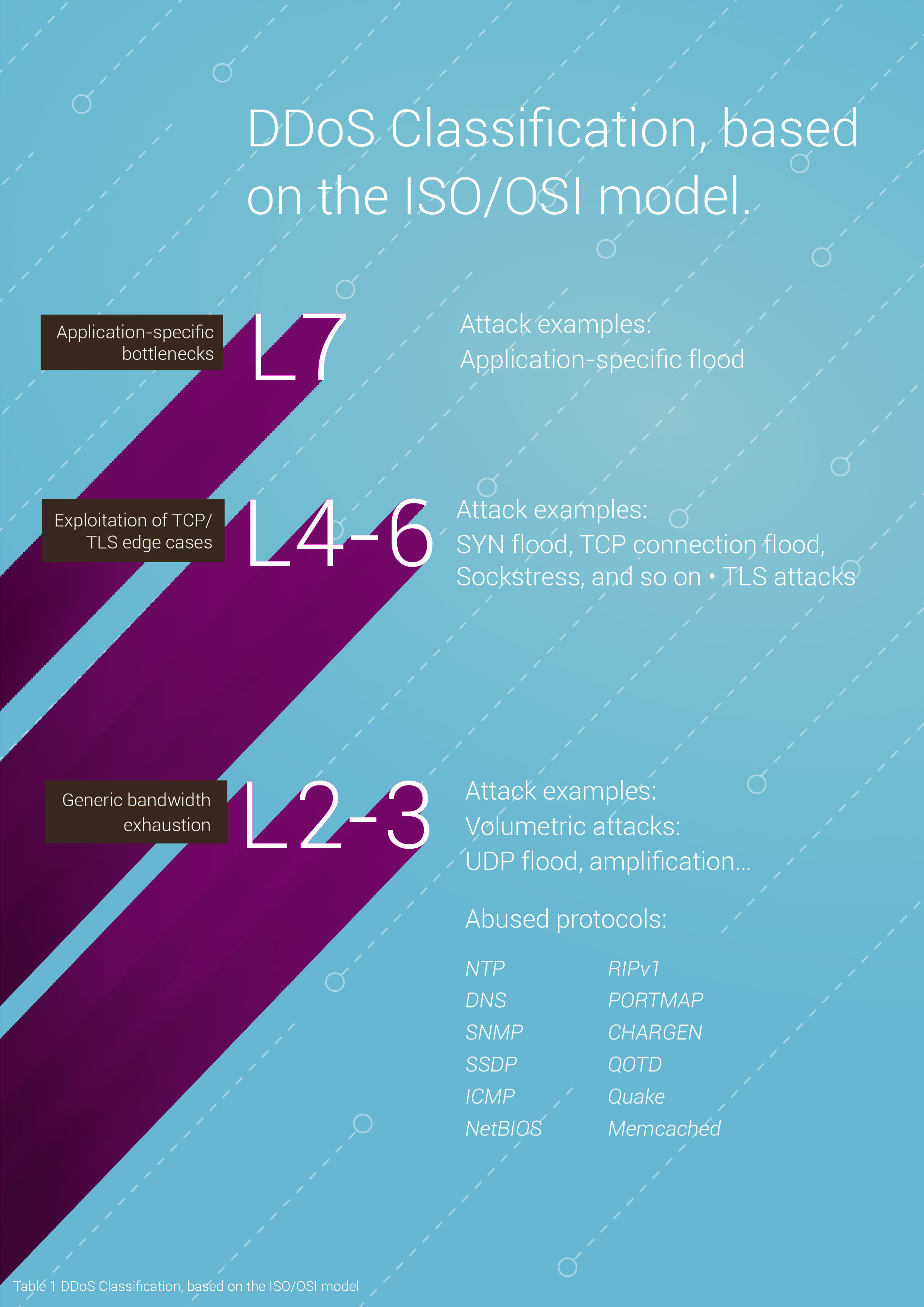
DDoS attacks are most common at layers 2-3, 4, 5, and 7 of the Open Systems Interconnection (OSI) model, which is described in Table 1.
Layer 2, 3 and 4 attacks correspond to the Link, Network and Transport layers of the OSI model: This document refers to these as infrastructure layer attacks.
Some examples of types of attacks are SYN Floods, UDP Floods, IP/ICMP fragmentation, NTP/DNS / SSDP amplification and SMURF.
This paper does not address application layer attacks (L7) or attacks that target SSL/TLS since they should be mitigated by different means.
Network and data center infrastructure are prime targets. If an attacker can fill network capacity or overwhelm routers and switches, legitimate traffic cannot get through.
Don’t overestimate your infrastructure:
Your current edge network hardware may serve your normal day-to-day needs but may fail rapidly during a DDoS attack if there is inadequate protection from a malicious event.
Determine and ensure that your infrastructure has sufficient balance with buffers above and beyond normal peak requirements.
Consider your tolerance for risk. A typical DDoS attack generates less than 10 Gbps, but peak DDoS traffic can exceed 1500 Gbps.
To evaluate their situation, network operators should consider these vital questions:
- Have you ever blackholed traffic to a customer site under DDoS attack?
- What DDoS protection do you have in place?
- How are you prepared for targeted attacks, 0-day threats and new attack vectors?
- How much available capacity do you have across your network, over regular peak traffic?
- If your network is hit with 10 Gbps of traffic from a reflection DDoS attack with hundreds of sources, how long will it take you to block it using an access control list (ACL)?
- How large of a DDoS attack will you attempt to mitigate before you decide to blackhole all traffic to that site?
- If a customer’s traffic is blackholed due to a DDoS attack, what requirements must be met before you restore their Internet service?
Infrastructure layer attacks
Infrastructure layer attacks assault either the link, network, or transport layers (OSI layers 2-3 and 4). The goal of such attacks is to cause network saturation by occupying as much as possible of the available bandwidth, which is typically measured in gigabits per second (Gbps).
“Network Time Protocol (NTP) was the first protocol being abused (back in 2013) as an amplifier in DDoS execution. With hundreds of thousands of NTP servers deployed all over the web, this particular vector was quite lucrative for the attackers looking for a way to amplify their capabilities. By early 2014, NTP replaced DNS as the primary reflection/amplification vector. The Smurf and Fraggle attacks also used amplification for DDoS and go back to 1999.
In 2015, we saw the rise of botnets on a mass scale. They used UDP-based amplification creating the largest volumetric DDoS attacks ever observed. The combination of thousands of compromised devices with the NTP and DNS amplification made these attacks highly dangerous, as the Dyn and OVH denial of service in 2016 showed. Joint disruption of the command and control (C&C) servers for those botnets made it possible to avoid the danger of botnets taking over the web.”
Qrator Labs CTO for the APNIC blog: “Understanding the facts of memcached amplification attacks”.
The most common DDoS attacks, User Datagram Protocol (UDP) amplification/reflection attacks and SYN floods, are infrastructure layer attacks. Attackers use these methods to generate large volumes of traffic that can exhaust the capacity of a network or a system like a server, firewall, IPS, or load balancer. These attacks have clear signatures that can make them easier to detect. Effective mitigation of these attacks requires network or system resources that exceed the volume generated by the attacker, effectively meaning that the traffic is directed to a safe place beyond the borders of the protected networks. Those resources do not actually belong to the customer — they belong to the given ISP or other infrastructure owner.
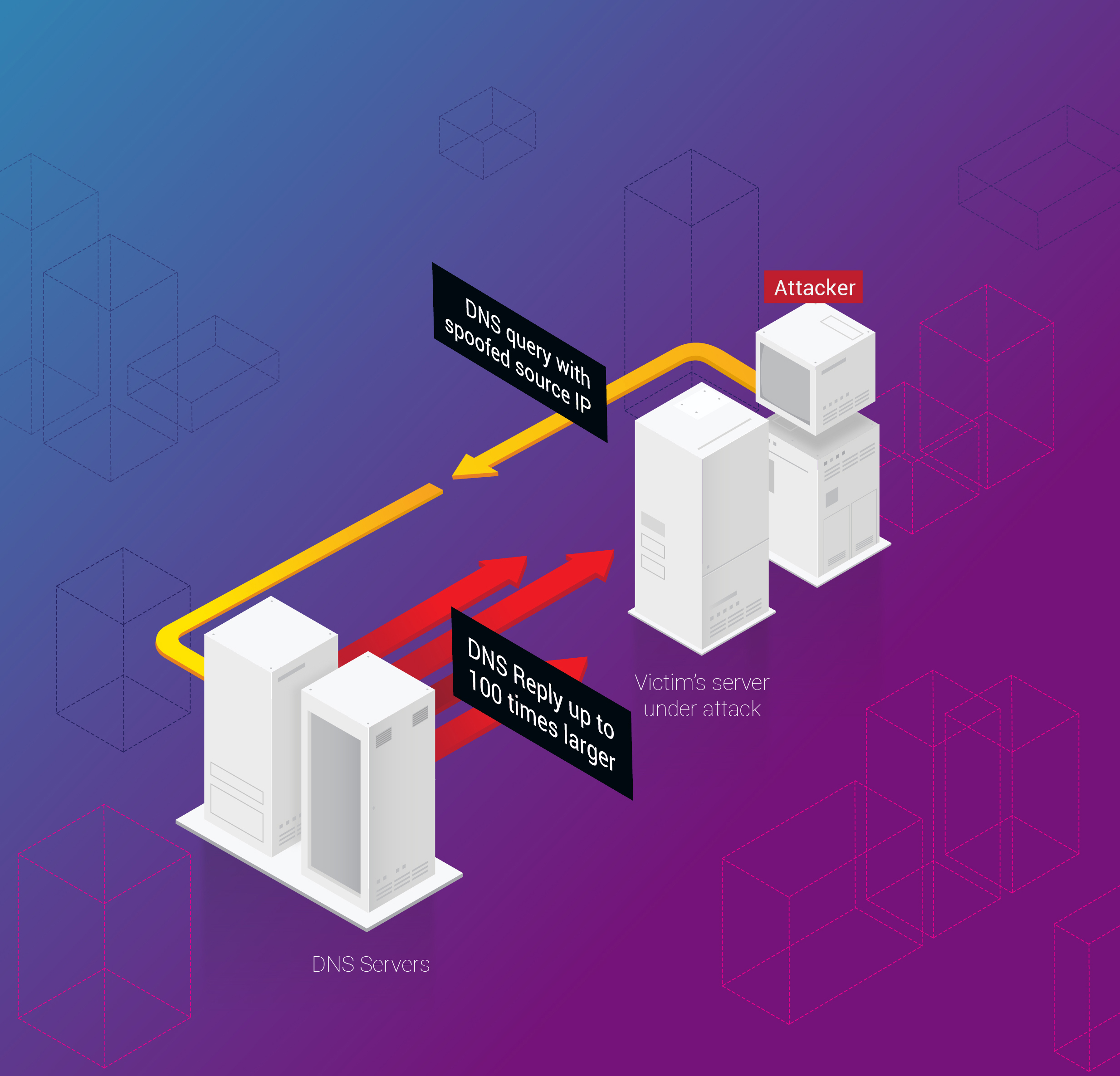
UDP, as a stateless protocol, can allow attackers to spoof the source of a request sent to a server in order to elicit a larger response. The amplification factor, which is the ratio of response size to request size, varies depending on the protocol used, such as Domain Name System (DNS), Network Time Protocol (NTP), or Memcached. For example, the amplification factor for DNS could be up to 179x—which means an attacker can send a request payload of 64 bytes to a DNS server and generate over 11456 bytes of unwanted traffic. With memcached the amplification factor has topped 50000x.
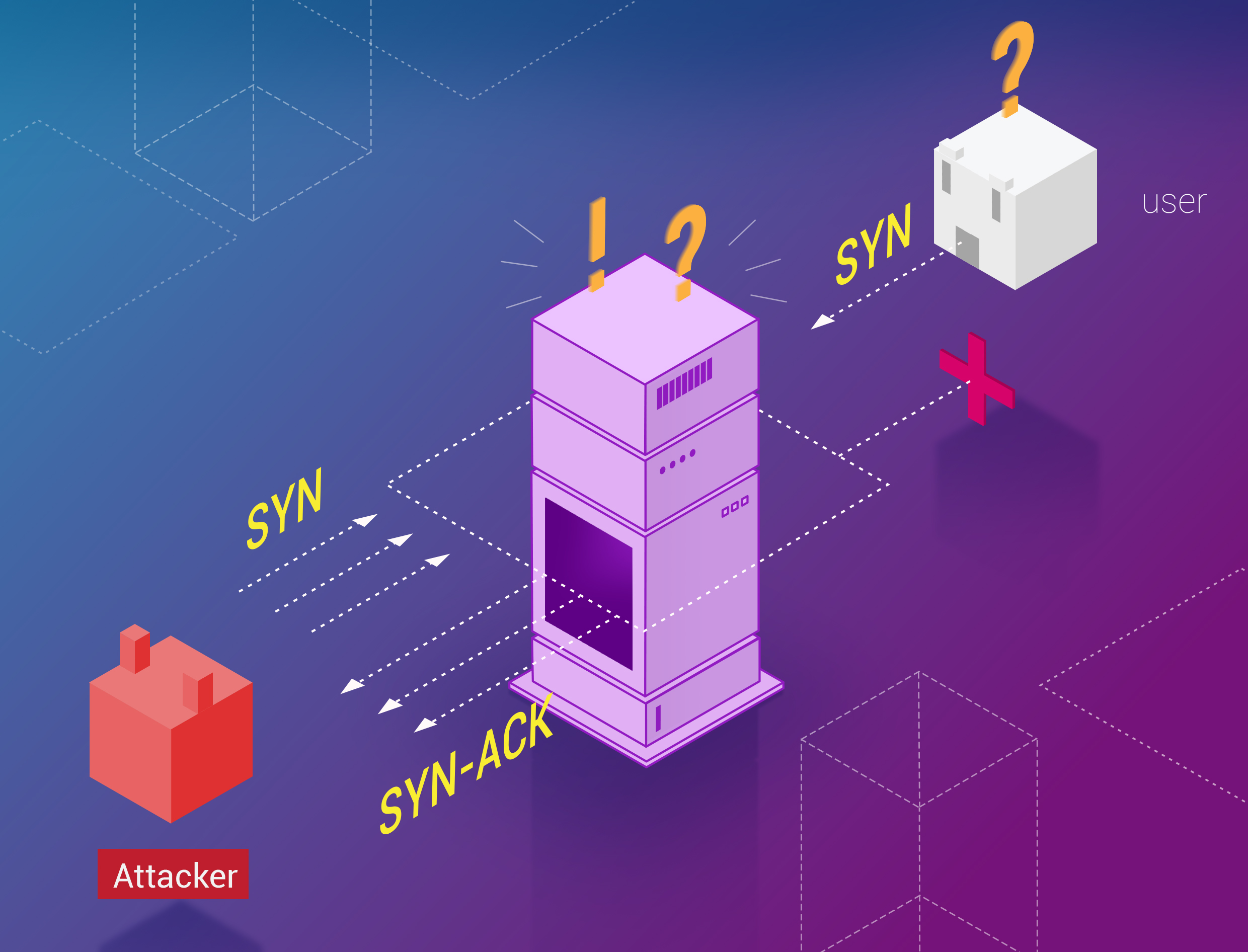
SYN floods can be in the order of tens of Gbps, but the attack intends to exhaust the available resources of a system by leaving connections in a half-open state. As illustrated in Figure 4, when an end user connects to a TCP service, like a web server, the client would send a SYN packet. The server would return SYN-ACK, and the client would return ACK, completing the three-step handshake.
In a SYN flood, the ACK is never returned, leaving the server waiting for a response and preventing new users from connecting to it.
DNS and NTP topped the 2017 list of DDoS attack vectors with the highest amplificator counts. Infrastructure-related attacks such as these accounted more than 99% of DDoS traffic, which is typical of recent quarters. Infrastructure attacks dominate as the standard method used by attackers. The barrier to entry for someone to launch a DDoS attack, particularly at the infrastructure layer, is incredibly low right now. Anyone with interest and access to a search engine can find the resources needed to launch volumetric DDoS attacks with minimal cost or effort.
Amplificators count
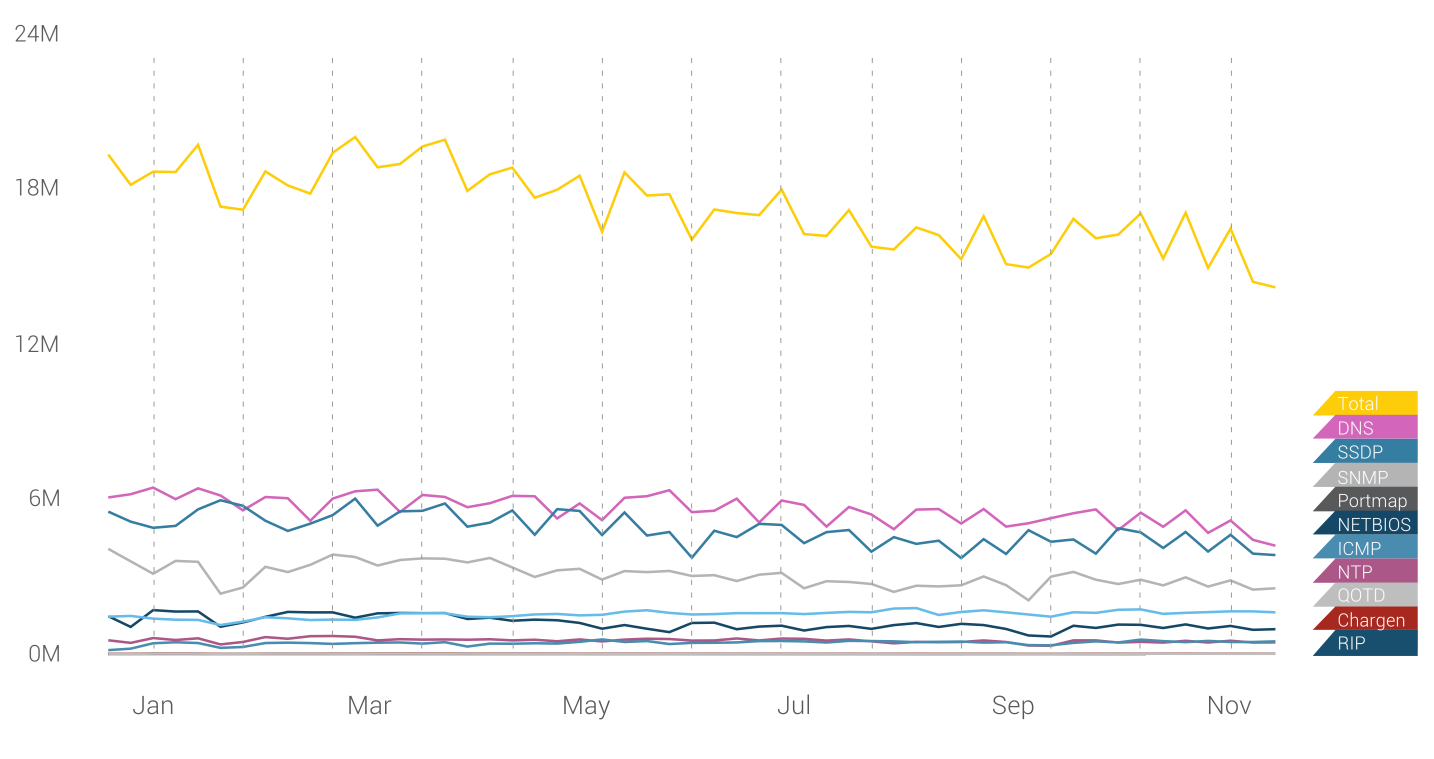
The current outlook is grim, as the latest events during 2018 (1,7 Tbps memcached amplification DDoS) show that old vulnerable servers and services are being replaced too slowly while new equipment with stronger capabilities keep entering service for the attackers. Each year a new vulnerability appears and, with the growing number of IoT appliances, next level attacks are always stronger, more capable and better distributed. Every day responses and solutions to existing threats become outdated and new vulnerabilities are identified. As of 2018, there are no signs of general improvement as those amplificators might also represent the core (in case of the DNS) of internet infrastructure, which must be handled gently.
System administrators need to continually apply security patches and ensure that systems are correctly configured. All exposed configurations should be reviewed on a regular basis or assigned to a vendor partner that does so. You could learn more on the memcached amplification and spoofed attacks from the talk at RIPE76 given by the CTO of Qrator Labs.
Infrastructure layer mitigation
The evolution of infrastructure layer attack mitigation began with the blackhole option – the complete drop of all traffic on the destination address. Discarding all packets at the routing level and using a routing protocol to implement changes on many devices at once has been the primary DDoS attack mitigation option for more than a decade. With virtually no impact on performance, null routing all traffic to the destination under attack is available to any company or person and history has shown multiple times how victims (Brian Krebs in the Mirai attacks) got blackholed, shifting out of everyone’s reach.
The introduction of BGP flowspec in 2009 did not have a positive impact since the protocol was under development for 6 years and as of early 2018 implementation is not as high as everyone anticipated. Further hindering the distribution of flowspec are the cost and lack of availability from upstream providers.
Also in 2009, the remote-triggered blackhole filtering option was introduced, which enables mitigation of DDoS-attacks by distributing discard routes based on the source or destination addresses of unwanted traffic among edge routers, as well as the classic destination path to the victim. On the “destination” level this option equals traditional blackholing, while on the “source” it isn’t capable to efficiently mitigate spoofed attacks. Besides that there is always the danger of overflooding edge routers upstream capacity - an action that would compromise any attempts to blackhole attack traffic.
Presently, none of these options entirely mitigates huge volumetric attacks.
Qrator.Ingress infrastructure is DDoS-resilient by design with the ability to automatically detect and filter excess traffic. To protect the availability of your infrastructure, it is necessary to implement architecture that allows you to take advantage of these capabilities. Two main features of the Ingress mitigation network are high on-demand scalability and globally distributed load-balancing.
One of the most common Qrator.Ingress use cases is an Internet Service Provider, Hoster and especially the Transit Provider, that serves customers and is primarily interested in protecting its own network from incoming attacks. Large amount of attacks is generated with goal to deal as much collateral damage as possible: to providers, clients and connected infrastructure.
Infrastructure Layer Defence
In a traditional data center environment, you can mitigate infrastructure layer DDoS attacks by using techniques like overprovisioning capacity or deploying DDoS mitigation systems. Infrastructure Layer Defence On the contrary with Qrator.Ingress, you have options for architecting your network to scale and absorb higher volumes of traffic without capital-intensive investments or unnecessary complexity. Critical considerations in the mitigation of volumetric DDoS attacks include the availability of transit capacity and diversity.
That is why Qrator.Ingress networks with multiple Points-of-Presence announcing BGP-Anycast paths, balancing the load naturally by smoothing the number of requests on each node, meaning globally consistent availability of a protected network, where only legitimate traffic reaches its destinations.
Qrator.Ingress offers only inbound traffic filtering. This is essential as not all companies are interested in scrubbing outbound traffic. For content providers, there could be a considerable multiplier of outbound traffic compared to inbound. For transit operators filtering outbound traffic is unnecessary and costly. Another reason for the exclusively inbound installation is the case of asymmetric traffic flow where there could be no outbound traffic at all - the data could follow another path. Since many companies do not have their own applications, they rent or resell their networking infrastructure in many forms - they should think first and foremost of its stability.
Qrator.Ingress is available in multiple locations worldwide. Scrubbing inbound traffic in each region, Ingress provides access to a unique set of Internet connections and peer relationships that allow for optimal latency and throughput to closely situated end-users.
It is also important to recognize the importance of filtering center location to DDoS resiliency. Many regions are located near Tier-1 operators connection paths. DDoS attacks often originate internationally, so it is helpful to be connected to Tier-1 ISP, as biggest operators maintain peers with other international carriers and larger peers, like internet exchanges. This helps end-users reach your application during periods of unusually large traffic volumes.
Massive DDoS attacks can exceed the size of a single upstream connection. To mitigate these attacks, we actively perform load balancing for any excess traffic. With this option, we reduce the risk of overloading your connection by distributing traffic across many channels. Qrator.Ingress global network 1,5 billion packets per second Service blocks attack within 30 seconds.
Access to multiple highly scaled internet connections can significantly increase your ability to optimize latency and throughput to end-users, absorb DDoS attacks, and isolate faults while minimizing any impact on availability.
Many common DDoS attacks, like SYN floods or UDP reflection attacks, would be rejected by Ingress and not make it to your network. When Ingress detects these types of attacks, it automatically absorbs the additional traffic, but you would not incur any additional charges. Ingress is service agnostic, which means that any traffic, like TCP, UDP, SMTP, FTP, VoIP, and proprietary or custom protocols is processed in the same way.
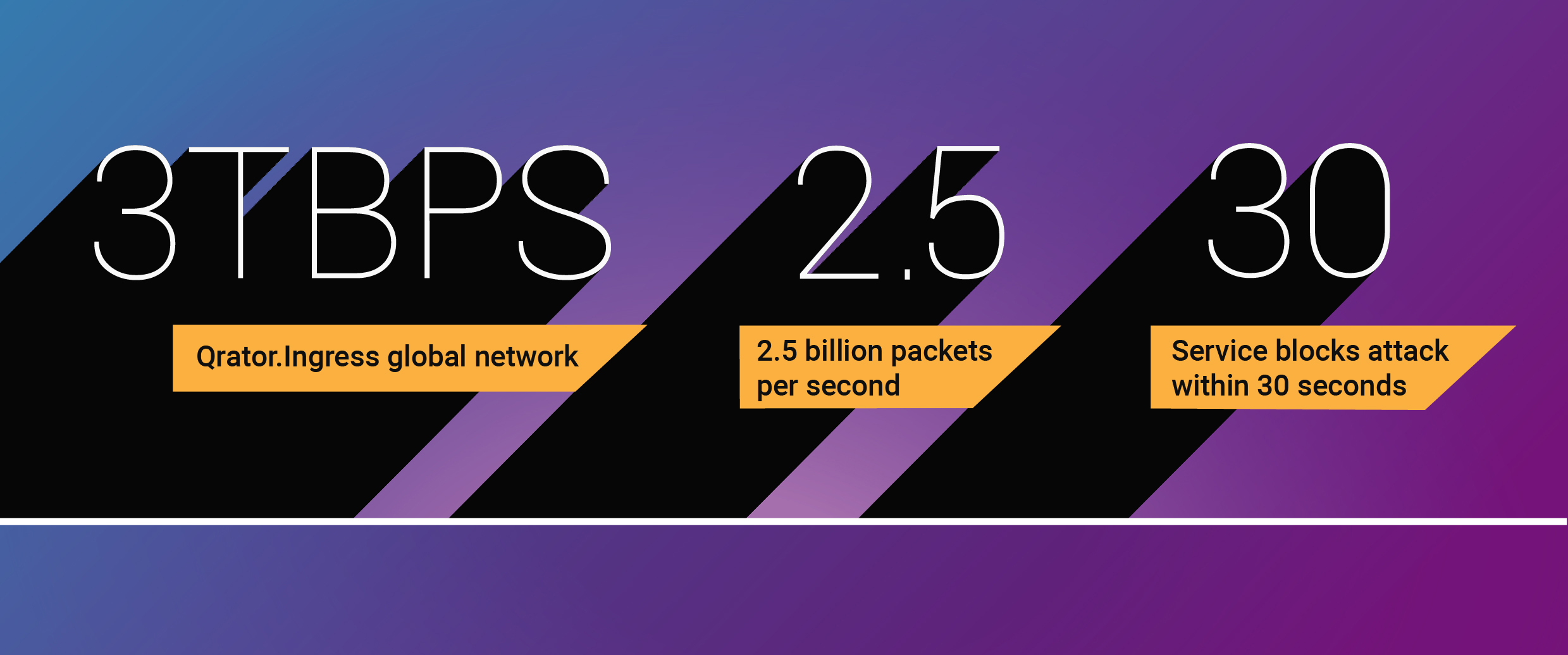
The Qrator.Ingress global network has over 2 Tbps (terabits per second) of scrubbing capacity and the ability to process 1,5 billion packets per second. Once activated, the service blocks attacks within 30 seconds. Real-time dashboards show attack traffic details, including vector types, traffic by PoP and IP range statistics.
Operational techniques
The mitigation techniques described in this paper allow you to architect networks that are resilient against network layer DDoS attacks. Generally, it is useful to know when DDoS attacks are targeting your application so that a proper response can be deployed. It may be advisable to engage additional resources to assess a threat or review the architecture of your application.
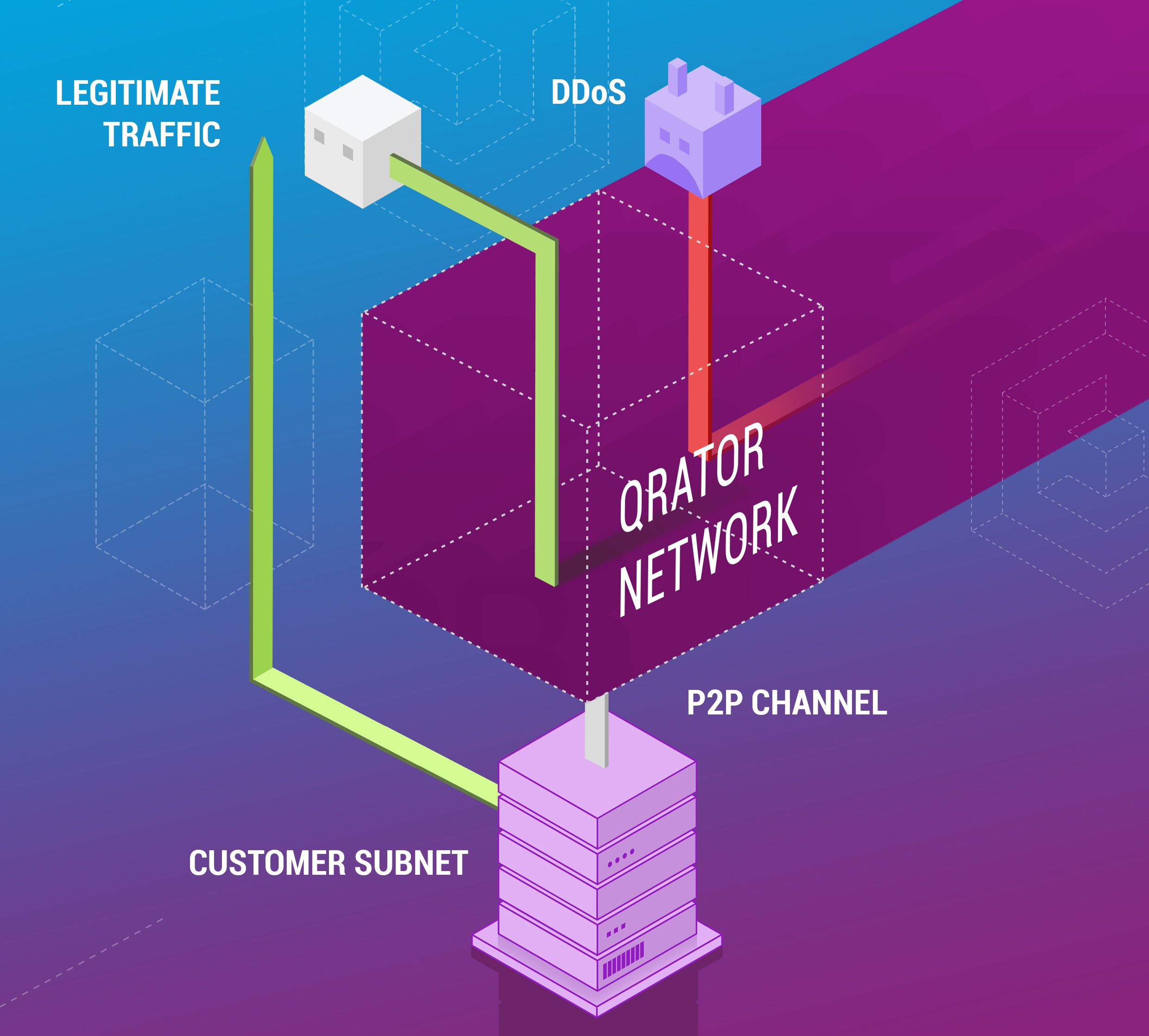
Qrator.Ingress uses BGP routing to enable infrastructure protection. BGP routing-based mitigation provides complete origin protection against direct-to-IP assaults for your network infrastructure. BGP routing is used to forward all traffic to the Qrator network, and this is done when Qrator.Ingress publishes and advertises the protected IP ranges. A dedicated physical channel, on the other hand, is used to connect Qrator scrubbing centers with the customer infrastructure, guaranteeing an uninterrupted secure connection.
Qrator.Ingress mitigation is available both as an always-on and an on demand service, with flow-based monitoring.
Qrator.Ingress protects entire networks by leveraging the Qrator Labs network with multi-terabit scrubbing capacity and high-capacity packet processing capabilities to instantly mitigate the most extensive L3-L4 DDoS attacks.
This service does not provide inspection and filtering of application layer (L7) DDoS attacks and does not guarantee the uptime of individual customer websites in protected networks.
Conclusion
With Qrator.Ingress, there is minimal effect on latency because a dedicated channel is established between the customer’s infrastructure and the nearest Qrator scrubbing center. Qrator’s global network of strategically located scrubbing datacenters ensures that the customer’s network is never far away.
The most important factor always comes down to time to mitigation—the amount of time that passes from the moment an attack is initially identified until it is mitigated. As long as the activating a service leads to minimal or no increased latency, an always-on, 24/7 security product is beneficial minimizing your time to mitigation—with no downtime.
The practices outlined in this paper can allow you to build a DDoS-resilient architecture that is capable of protecting your application against many common infrastructure and application layer DDoS attacks. The degree to which you architect your application according to these practices will influence the type, vector and volume of DDoS attacks you can mitigate. Qrator. Ingress encourages you to implement these best practices to better protect the availability of your application against common DDoS attacks.
2020 Update
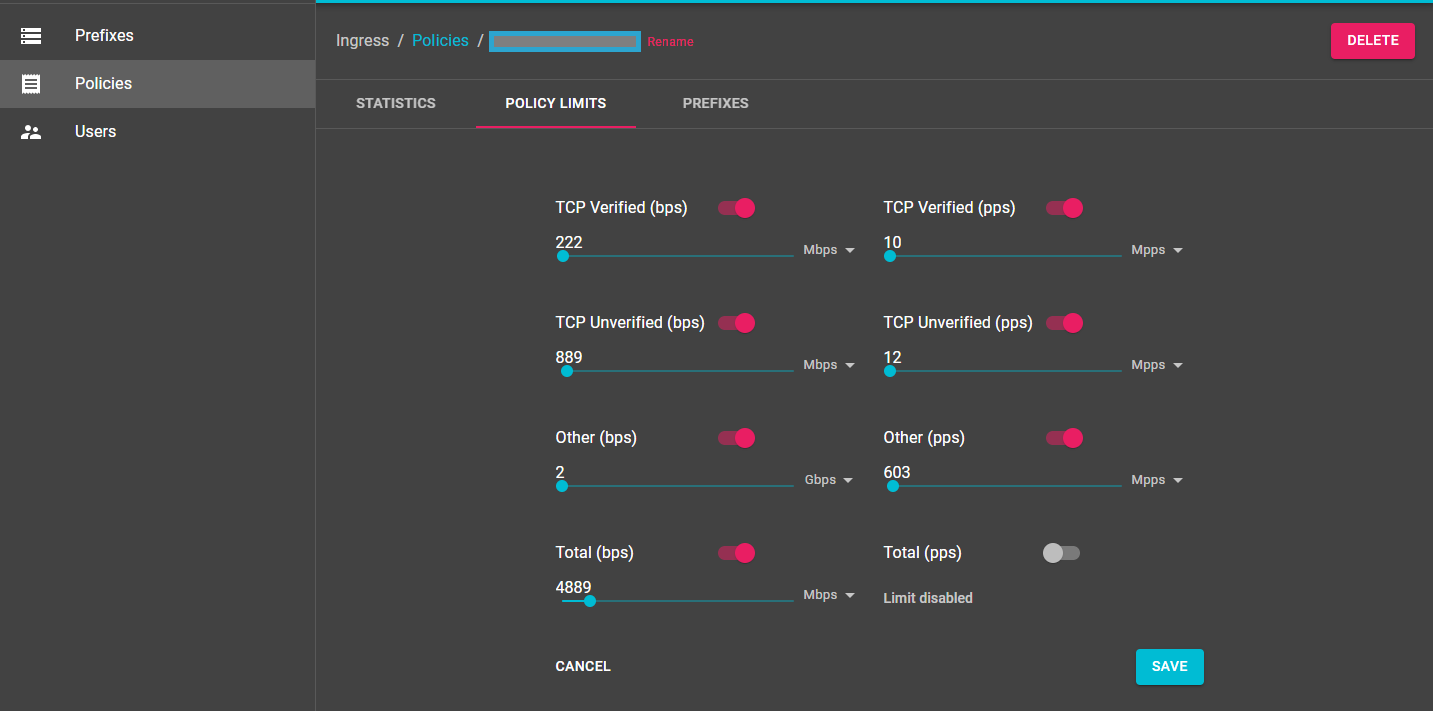
During 2019 we deployed an improved version of the Ingress filtering service, which allows more precise fine-tuning and broader configuration. It is available to the end-user via informative yet straightforward interfaces. This newer Ingress service is already deployed on our leading filtering network, ready to serve customers seeking off-ramp traffic inspection.
Yandex.Cloud made it possible for us to go through a process we never attempted before — integrating two big clouds — and it was in an unconventional manner. We were able to integrate two infrastructures with the help of Qrator Labs physical nodes that were placed in the network of a partner and worked over his traffic.
As a result a newer, more deeply customizable version of the Ingress service is ready for use after extensive testing. We’ve built a state-of-the-art inbound traffic filtering service specifically designed for businesses with excessive amounts of outbound traffic.
The new Ingress service is easy to understand and implement by the end-user. It allows for customization of all the parameters that were identified during the extensive testing period.
