That is a quote from one of my favorite bands. Dave Gahan from Depeche Mode is a living proof that you can say the word “wrong” 65 times in 5 minutes and still be a rock star. Let’s see how that’s going to work for me.
That is a quote from one of my favorite bands. Dave Gahan from Depeche Mode is a living proof that you can say the word “wrong” 65 times in 5 minutes and still be a rock star. Let’s see how that’s going to work for me.
DDoS attacks mitigation in the wild requires various techniques to be tested and learned. Hardware and software network solutions need to be tested in artificial environments close to real-life ones, with massive traffic streams imitating attacks. Without such experience, one would never acknowledge the specific capabilities and limitations every sophisticated tool has.
In this article, we are going to disclose certain methods of traffic generation used in Qrator Labs.
DISCLAIMER
We notoriously advise any and every reader not to try any offensive use of the tools we write about in this research. Organization of DoS attacks is legally persecuted and could lead to lengthy imprisonment. Qrator Labs responsibly conducts all tests within an isolated laboratory environment.

During the World Cup 2018 active period traffic of online stores has decreased by almost 1.5 times. Online games and Forex sites attendance felt even stronger, Qrator Labs found. The days of Russian team’s plays made the drop even more pronounced and evident. Such dynamics are tied not only to the popularity of football matches but also the holiday season, explain market participants.
Originally this post has been published at the APNIC blog.
Cybersecurity attacks have become a weekly occurrence in many news columns. One recent example was that of one of our customers, QIWI payment system, successfully mitigating a 480 Gbps memcached amplified UDP DDoS attack.
While we at Qrator Labs would rather stay out of the news, such instances justify all the preparation that we put into mitigating for such attacks. To help others learn from our experience, I thought I’d recap several facts about amplification attacks, so that you too will be prepared ‘when’ the day comes.
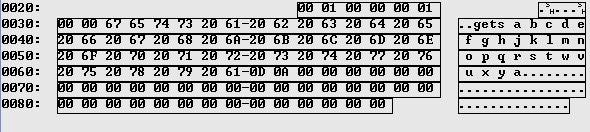
A long time ago in a git repository far-far away, a commit made by Brian Aker introduced a brilliant feature of the default listening to UDP traffic in memcached.
Days in between February 23, 2018, and the Monday of February 26, 2018, were marked by multiple memcached-amplification DDoS attacks across entire Europe.
As many readers of the Qrator Labs blog know, DDoS attacks target aims at different network levels. In particular, a substantial botnet presence allows an intruder to carry out attacks on the L7 (application layer) and mimic regular users. Without such a botnet the attacker is forced to limit packet attacks (any of those allowing the source address forgery at some stage of execution) to the underlying transit networks levels.
Naturally, in both these scenarios attacker tends to use some existing toolkit — just like a website developer does not write it entirely from scratch, using familiar frameworks like Joomla or Bootstrap (or something else depending on one’s skills). For example, the well-known framework for executing attacks from the Internet of Things for a year and a half is Mirai, open-sourced by its authors in an attempts to shake the FBI off the tail in October 2016.