Dive into Q2 DDoS and BGP Incidents Statistics and Overview.
Dive into Q2 DDoS and BGP Incidents Statistics and Overview.
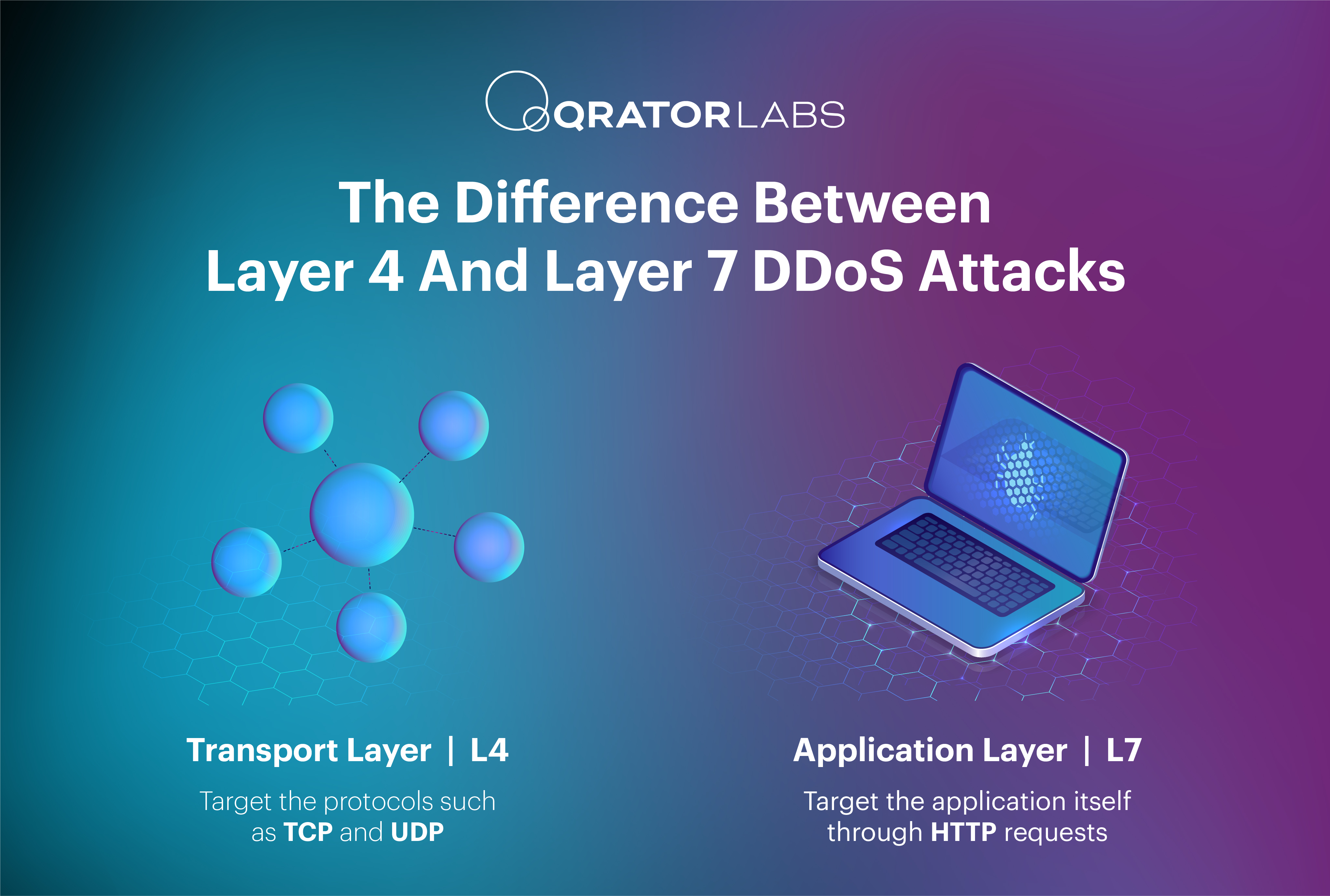
Learn about the distinct methodologies and impacts of layer 4 and layer 7 DDoS attacks, from SYN floods and UDP floods at the transport layer to HTTP floods and Slowloris attacks at the application layer. Understand how cybercrime services like booters facilitate these attacks and explore notable case studies, including the Dyn and GitHub incidents.
In our ongoing commitment to providing a convenient tool for everyday use, we are excited to announce a complete revamp of the UI/UX design of the Qrator.Radar web application.
Our team enjoyed working to create a more user-friendly interface, improved navigation, and better data visualization.
These updates aim to improve our users’ experience and simplify the processes of connectivity troubleshooting and network anomaly analysis.
These and other interesting features await you on our updated Qrator.Radar website.
Dive in and explore all the changes we've made firsthand.
CHECK OUT THE NEW LOOK

In August 2023, a vulnerability in the HTTP/2 protocol, known as CVE-2023-44487 or "Rapid Reset," was discovered. This article provides an in-depth understanding of how CVE-2023-44487 works, its impact on HTTP/2, and offers 4 mitigation strategies to defend against this vulnerability.
Discover how cybercriminals use fast flux to increase the resilience and takedown immunity of their malicious infrastructure. Understand the benefits of fast flux for attackers, the challenges it presents for security professionals, and the most effective strategies for combating this threat, such as domain seizures, botnet takedowns, and international cooperation.
Explore the history of DDoS attacks from their inception in 1994 to the sophisticated threats of the present day. Discover how bandwidth, processing speeds, and protection mechanisms have evolved, fueling the arms race between attackers and defenders. Understand the forces driving the evolution of DDoS tactics, from simple bandwidth overloads to complex amplification and application-layer attacks.
Explore essential strategies to safeguard your website against unauthorized AI data scraping while maintaining a superior user experience. Learn how rate limiting, robots.txt file, and selective IP bans can protect your digital assets.
The year 2023 turned out to be quite rich in events and trends in the field of cybersecurity. We witnessed a new term "white noise", the development of artificial intelligence led to increased bot activity, which significantly affected commercial companies. We detected signs of a resurgence in popularity of commercial DDoS attacks. The implementation of "remote office" technologies led to the expansion of communication channels and, as a result, increased intensity of attacks. But first things first.
The study delves into the Sustainability of National Internet Segments, revealing crucial insights into Internet reliability across countries.