We invite you to take a look to DDoS attacks mitigation and BGP incidents statistics recorded for the third quarter 2023.
We invite you to take a look to DDoS attacks mitigation and BGP incidents statistics recorded for the third quarter 2023.
We are excited to announce the launch of our brand new Qrator.Radar website.
We completely redesigned our backend, having unified it for both Real-time BGP monitoring and the new radar.qrator.net site. This brings several advantages, including improved data consistency and performance.
We invite you to take a look to DDoS attacks mitigation and BGP incidents statistics recorded for the second quarter 2023.
Let's take a deeper look at the Q1 2023 DDoS attacks mitigation statistics and observations from Qrator Labs' perspective.
Now that 2022 has come to an end, we would like to share the DDoS attack mitigation and BGP incident statistics for the fourth quarter of the year, which overall saw unprecedented levels of DDoS attack activity across all business sectors.
In 2022, DDoS attacks increased by 73.09% compared to 2021.
Let's take a closer look at the Q4 2022 data.
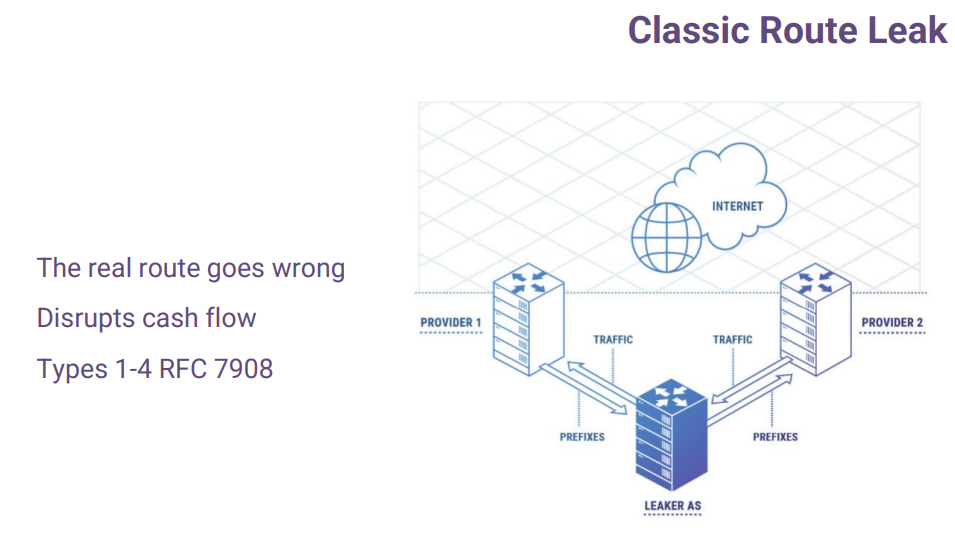
All the credit is due to the RFC’s authors: A. Azimov (Qrator Labs & Yandex), E. Bogomazov (Qrator Labs), R. Bush (IIJ & Arrcus), K. Patel (Arrcus), K. Sriram.
According to RFC7908: “A route leak is the propagation of routing announcement(s) beyond their intended scope. That is, an announcement from an Autonomous System (AS) of a learned BGP route to another AS is in violation of the intended policies of the receiver, the sender, and/or one of the ASes along the preceding AS path. The intended scope is usually defined by a set of local redistribution/filtering policies distributed among the ASes involved. Often, these intended policies are defined in terms of the pair-wise peering business relationship between ASes (e.g., customer, transit provider, peer).”
Eugene Bogomazov from Qrator Labs presented a paper during the African Peering and Interconnection Forum that took place on August 23, 2022. The paper highlights the results and conclusions of measurements taken from several networks in African countries. We publish these results here through this blog.
In this research, Qrator.Radar team evaluated the African Internet segment and its current state: how many ISPs operate in the region and their relations. Also, the study highlights routing security metrics and transit reliability.

With the end of the 2022' third quarter, we invite you to take a tour into DDoS attacks mitigation and BGP incidents statistics recorded from July to September.
The National Internet Segment Reliability Research explains how the outage of a single Autonomous System might affect the connectivity of the impacted region with the rest of the world. Generally, the most critical AS in the region is the dominant ISP on the market, but not always.
As the number of alternate routes between ASes increases (the "Internet" stands for "interconnected networks" - and each network is an AS), so does the fault-tolerance and stability of the Internet across the globe. Although some paths are more important than others from the beginning, establishing as many alternate routes as possible is the only viable way to ensure an adequately robust network.
The global connectivity of any given AS, whether an international giant or a regional player, depends on the quantity and quality of its path to Tier-1 ISPs.
Usually, Tier-1 implies an international company offering global IP transit service over connections with other Tier-1 providers. Nevertheless, there is no guarantee that such connectivity will always be maintained. For many ISPs at all "tiers", losing connection to even one Tier-1 peer would likely render them unreachable from some parts of the world.
The second quarter of the year has ended and, as usual, we take a look back at the mitigated DDoS attacks activity and BGP incidents that occurred between April and June 2022.